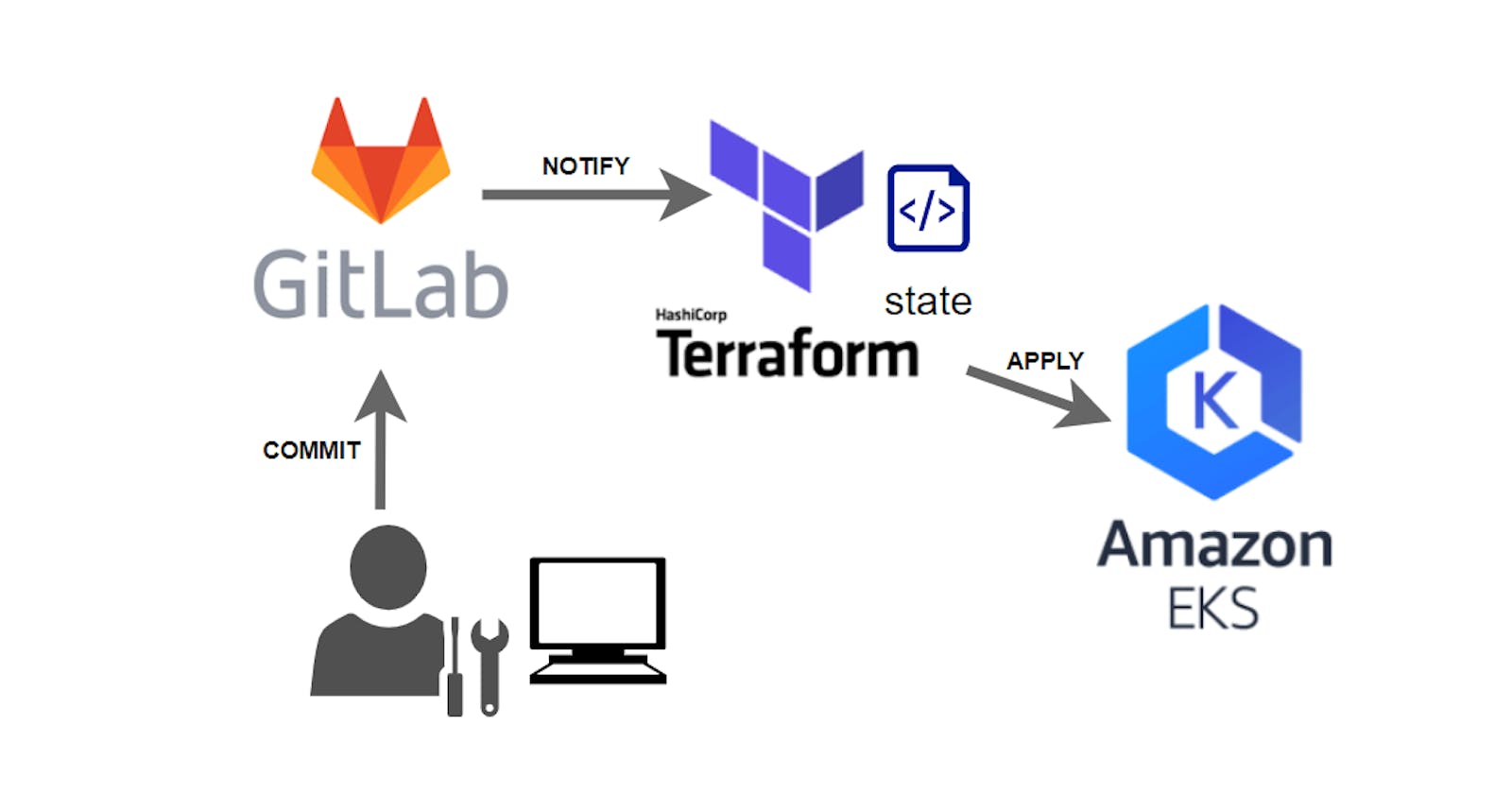
On this page we will show you how to setup CI/CD between your Git provider and Terraform Cloud to deploy automatically a Kubernetes cluster on AWS EKS !!!
Go read this page if you want to know Why do we want to use a Remote state provider like Terraform Workspace?
Here is the summary of what we are going to do:
Prepare your AWS IAM account and policies for EKS deployment
Prepare your Terraform Cloud Workplace for remote state
Create your EKS cluster with remote state
Setup your Terraform Cloud Workplace with your Git provider
Create your EKS cluster using remote state and CI/CD
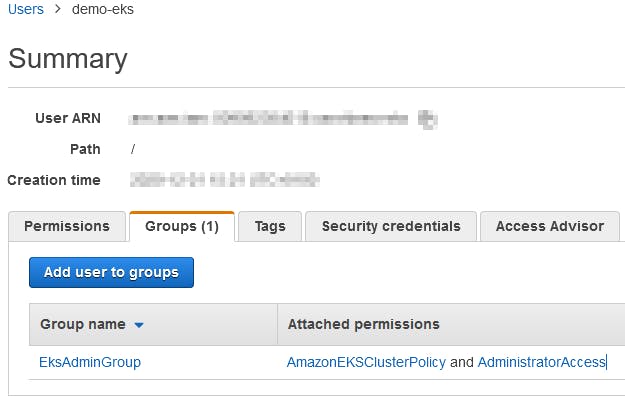
First we will create a new IAM user demo-eks with Programmatic access and the rights to use all the stuff needed to create an EKS cluster in a brand new VPC.
It is not easy to find out which rights and policy is needed and it depends on you environment. These right below will always work. You will probably need to limit these rights, particularly with regard to administrative rights.
We create a new EksAdminGroup group with these two AWS Managed policy AmazonEKSClusterPolicy and AdministratorAccess.
Then we add the demo-eks user to this new EksAdminGroup group.
Next step will be to setup the Workspace in Terraform Cloud.
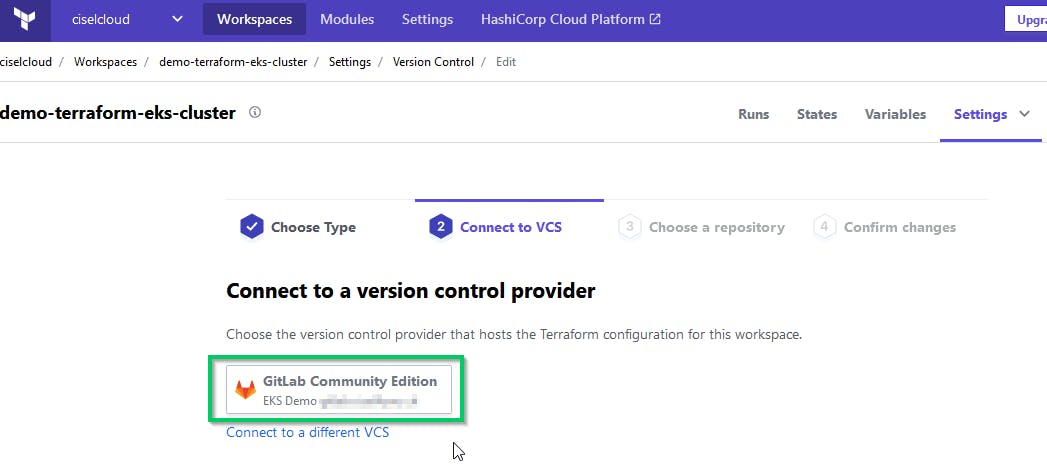
Create an account on app.terraform.io and then link you Github or Gitlab Version Control System (VCS) with your Terraform Cloud.
To do so, simply follow the Terraform documentation below:
VCS Integration : terraform.io/docs/cloud/vcs/index.html
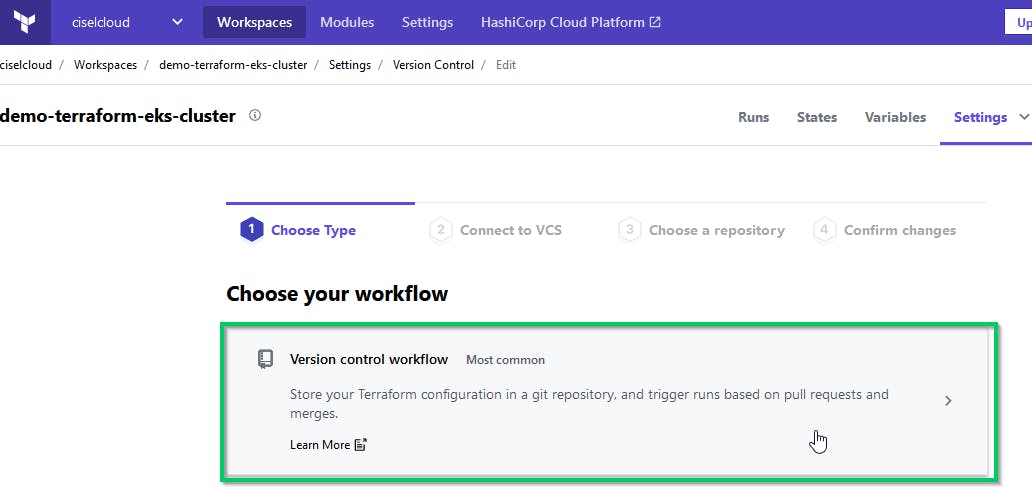
After you successfully added your VCS we will create a Terraform Workspace.
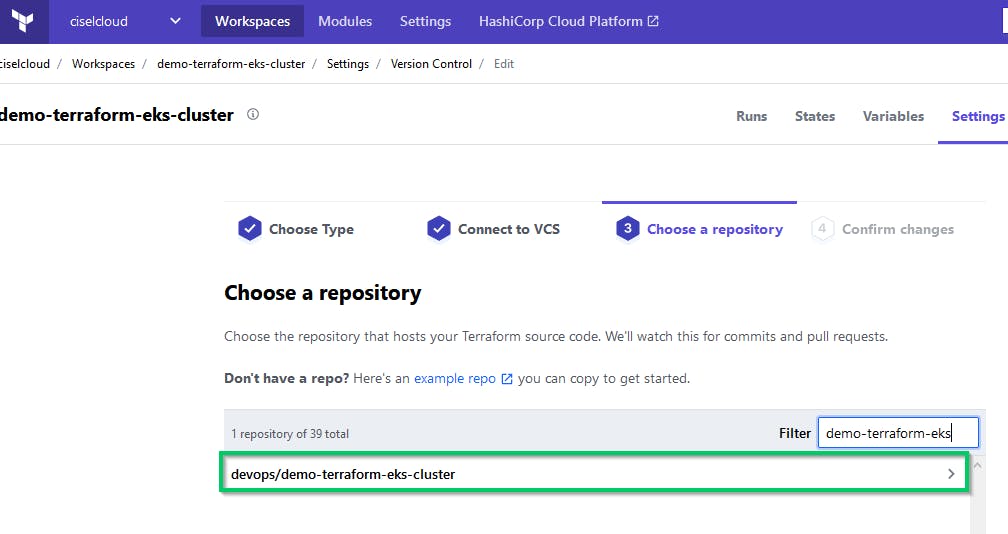
You need to clone our eks-terraform-demo Public Repository and to push it to your Git. When this is done, you can create a Workspace and select the newly created repo in the list.
Choose Workflow with the type Version Control
Connect it to your VCS
Select the repository of the project
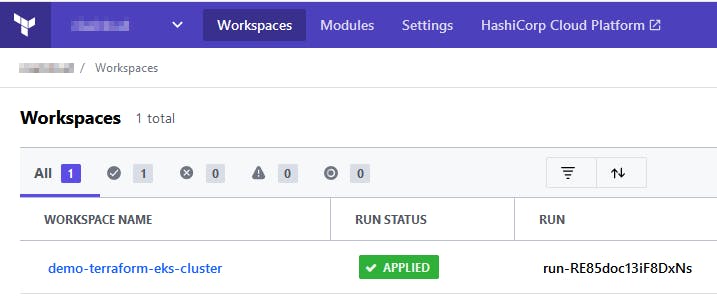
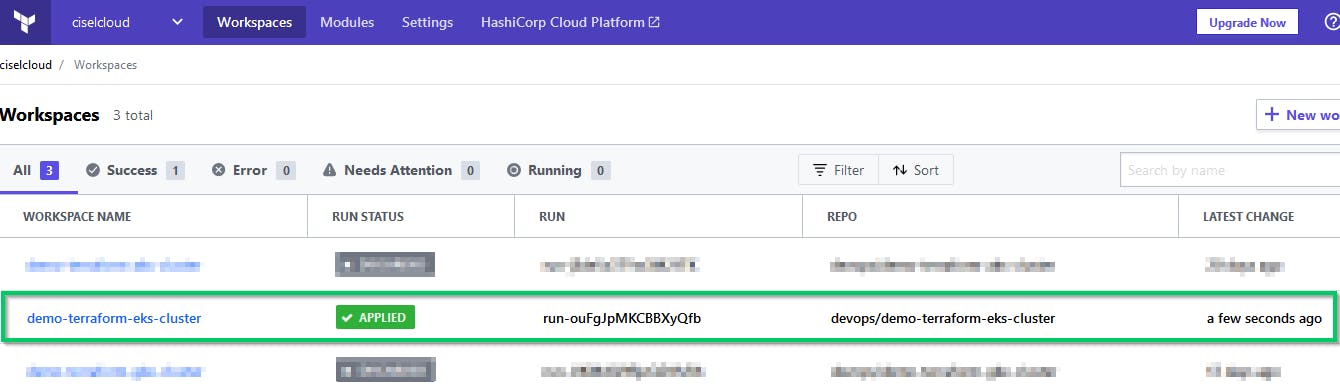
The Workspace will take some time to synchronize. When everything is good you will see it in the list.
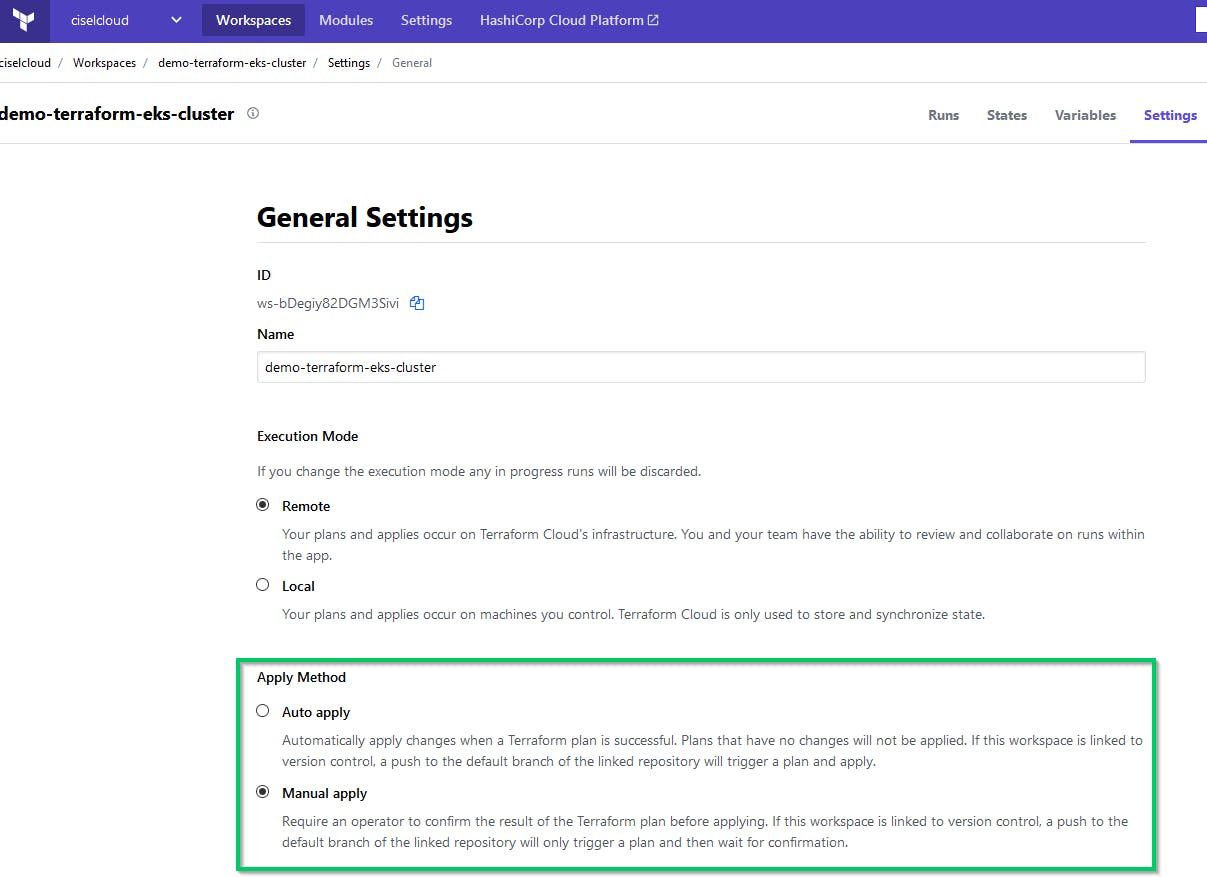
In the General settings of the Workspace, choose if you want to apply automatically every new changes that are applied in your repo or if you want to validate them manually before to apply.
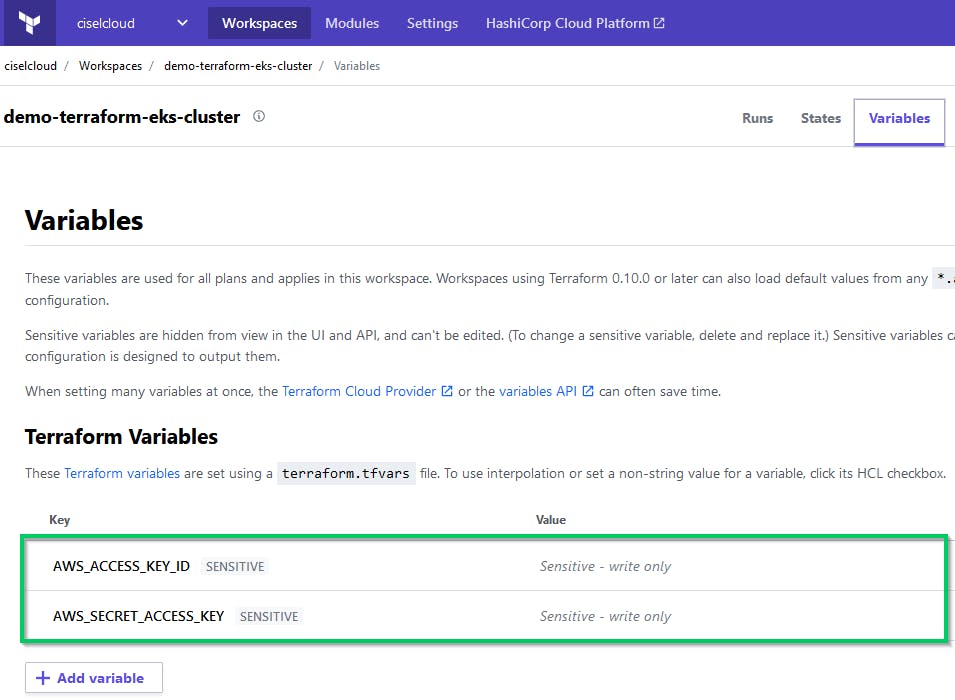
Next we need to create Terraform variables that will be used to connect to your AWS in order to create the cluster and all the resources needed.
Use the values of the AWS_ACCESS_KEY_ID and the AWS_SECRET_ACCESS_KEY for the demo-eks user and put them in variables of your Workplace. Set these variables as sensitive. Terraform Cloud creates an ephemeral VM to run Terraform operations (which create and manage your infrastructure).
It's time to adapt some values to be able to run this project.
Don't forget, we are in some kind of a GitOps CI/CD mode, so every time you commit it will notify Terraform Cloud that there are new changes to apply to the infrastructure.
demo-eks-backend.tf : Fill with your Terraform values
terraform {
backend "remote" {
organization = "your-terraform-organisation"
workspaces {
name = "your-terraform-workplace"
}
}
}
demo-eks-vpc.tf : Change the AWS Region if needed
...
variable "region" {
default = "eu-west-3"
description = "AWS region"
}
provider "aws" {
version = ">= 2.28.1"
region = "eu-west-3"
}
...
Commit your changes
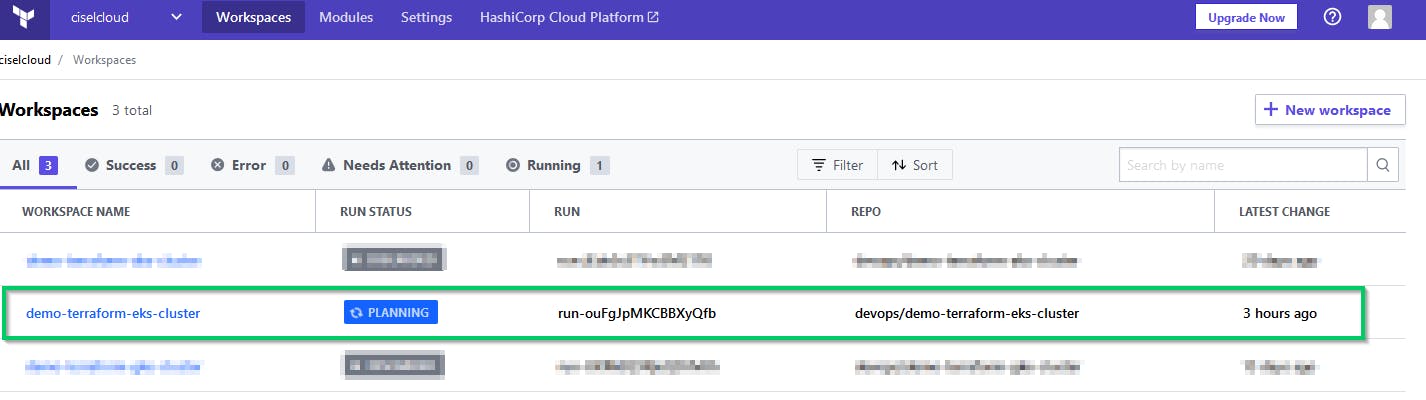
You can see the status of the RUN in the Terraform Cloud web UI.
First it will be in a **PLANNING ** state
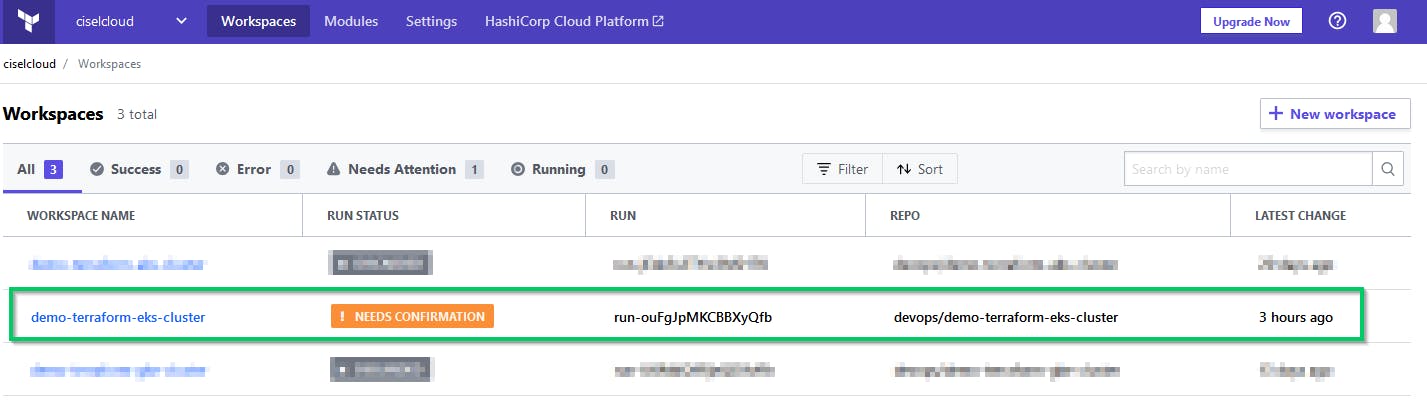
Then automatically to the **! NEEDS CONFIRMATION ** state
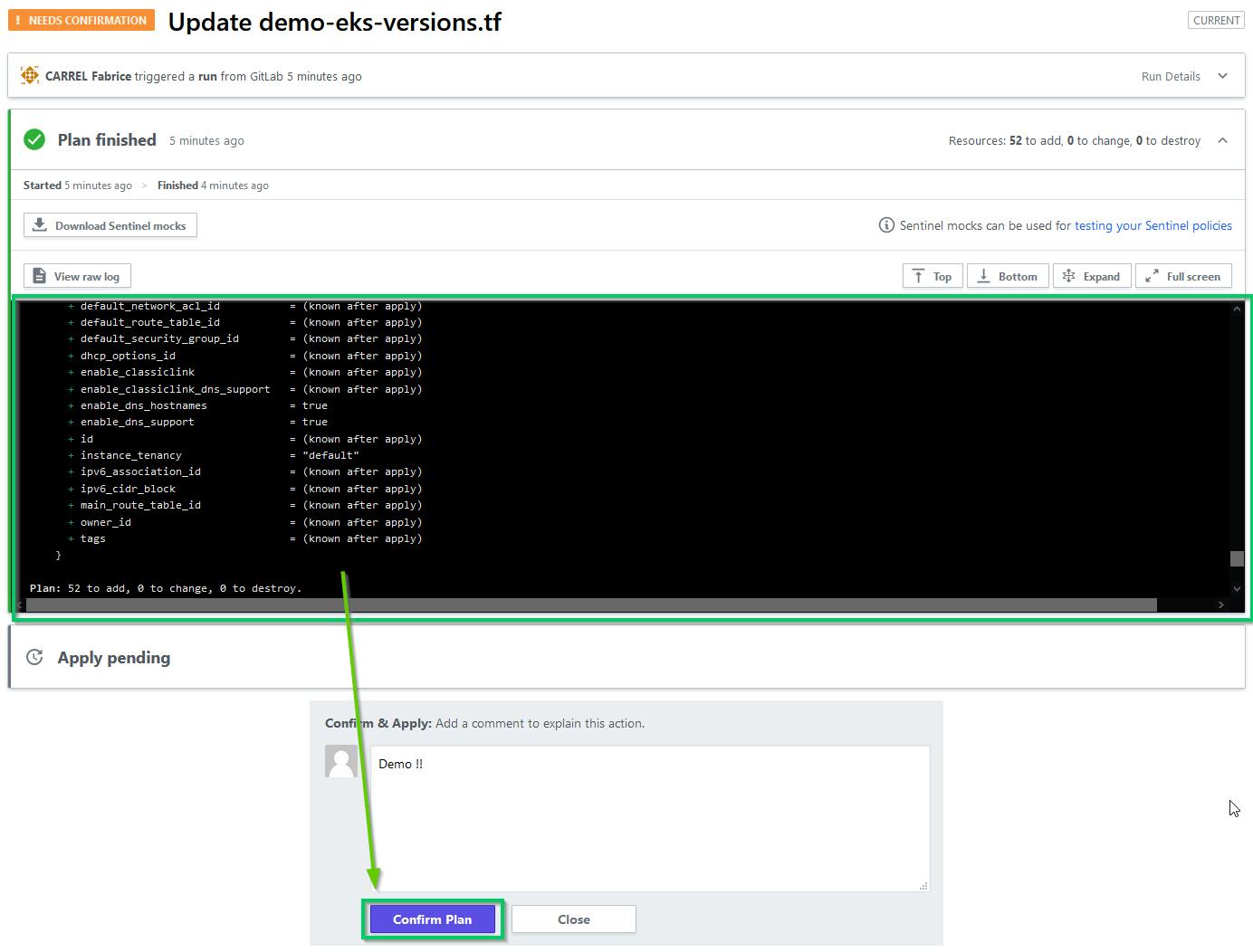
After reviewing the plan you can confirm it and the apply will start.
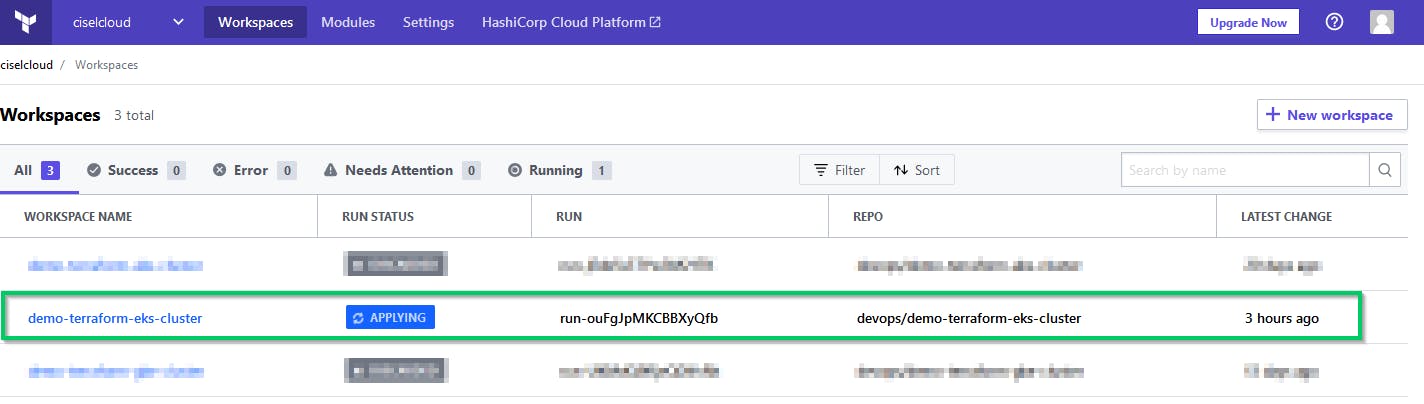
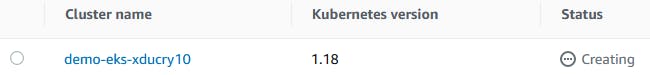
The deployment can take a few minutes. You can also check if the EKS cluster is in the creating state in AWS
When the run is finished the status goes to APPLIED
The final logs of the run contains the output of the kubeconfig that you can use to reach your cluster with kubectl.
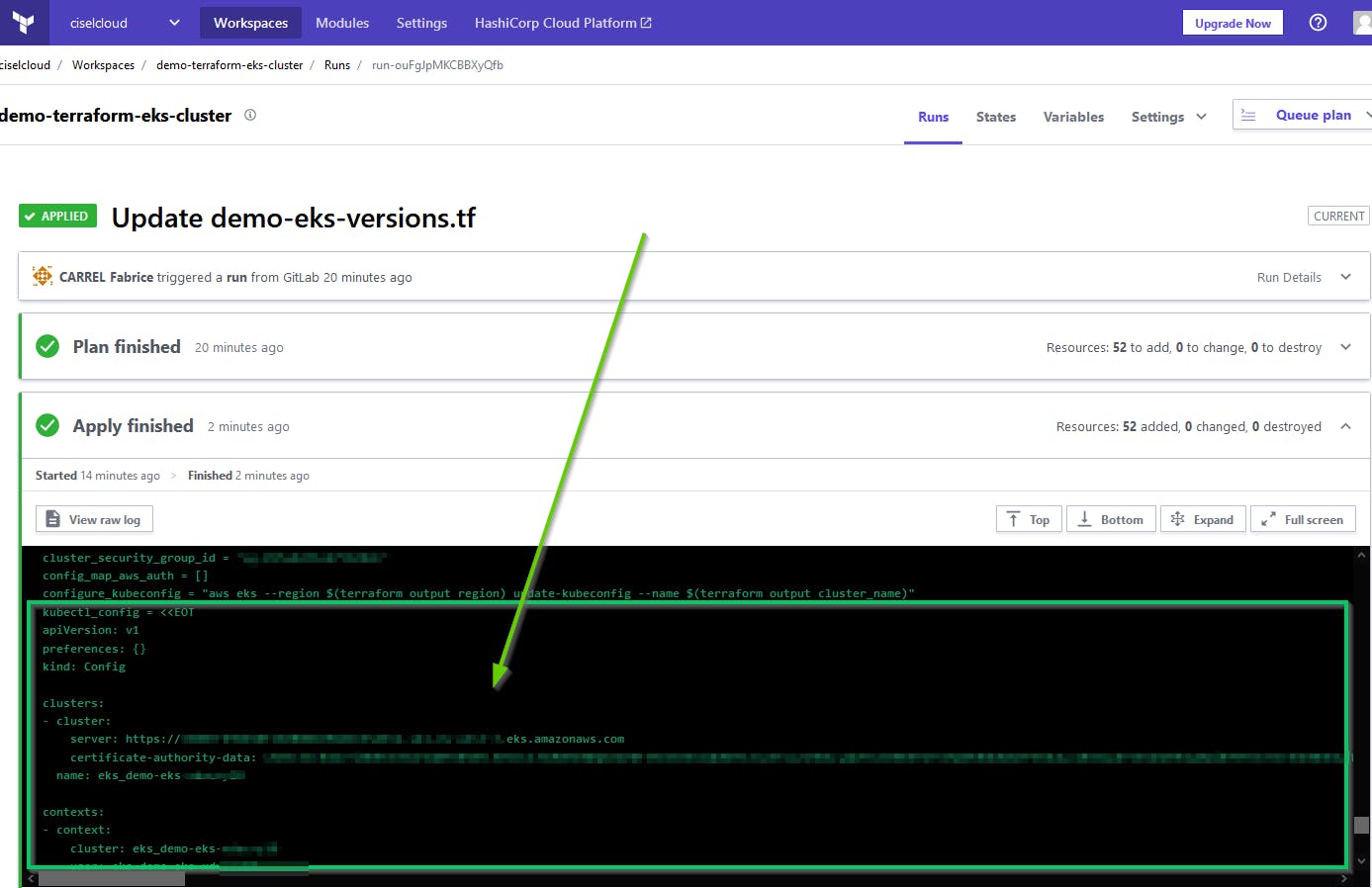
Or you can use the information in the AWS EKS console to access the new cluster !
Feel free to comment this article if you have any question